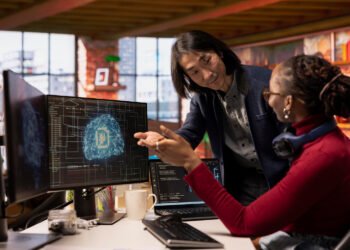
Cybersecurity has been the backbone of IT professional newsletters for a decade — but in 2026, the conversation has been dramatically transformed by AI on both sides of the battle. Attackers are using generative AI to craft hyper-personalized phishing emails, build adaptive malware, and discover zero-day vulnerabilities at machine speed. Defenders are deploying AI-powered Security Operations Centers (SOCs), behavioral anomaly detection, and automated incident response to keep pace.
The threat landscape has never been more sophisticated. Nation-state actors, ransomware-as-a-service groups, and supply chain attacks are operating at scale. The average cost of a data breach in 2025 reached $4.88 million (IBM Security), and mean time to contain a breach now averages 73 days. These numbers are driving urgent, board-level conversations about cybersecurity investment across every industry that LeadCrafters serves.
Why IT Leaders Are Obsessed With It
CISOs and Security Architects are navigating an impossible mandate: defend an exponentially expanding attack surface — cloud workloads, remote endpoints, SaaS apps, OT/IoT devices — with flat or shrinking security headcounts. AI-powered tools like Microsoft Sentinel Copilot, CrowdStrike Charlotte AI, and open-source SIEM integrations promise to bridge this gap. But procurement decisions require trust, proof of concept, and peer validation — creating enormous appetite for educational content, vendor comparisons, and real-world case studies.
Key Sub-Topics Driving Engagement
The most-clicked cybersecurity newsletter content in 2026 covers: zero-trust architecture implementation, AI-powered SOC automation, identity and access management (IAM) for hybrid environments, ransomware response playbooks, third-party vendor risk management, and regulatory compliance (DORA, NIS2, SOC2, ISO 27001). Each of these is a buying trigger — IT teams researching these topics are actively evaluating vendors.
Market Signals
Global cybersecurity spending is projected to exceed $300 billion in 2026. With 3.5 million unfilled cybersecurity jobs globally, automation tools that reduce analyst workload are in high demand. Cybersecurity newsletters consistently achieve 35–50% open rates — the highest of any IT sub-vertical — signaling an intensely engaged audience that actively reads and acts on content.